RFID card blockers protect your RFID cards from criminals out to skim your data. The blockers offer a cover that prevents RFID readers from capturing the signals produced by RFID cards.
The blockers are made from different materials that are poor magnetic conductors. They block RFID waves, eliminating any chance of the card being read by criminals.
But what is RFID skimming? How does it work? And why is it necessary to use RFIC card blockers to prevent card skimming?
If these are some of the questions that linger in your mind, this article offers comprehensive answers.
What is RFID Card Skimming?
RFID card skimming refers to the use of technology to obtain data from cardholders without their knowledge. This phenomenon is also called digital pickpocketing since criminals can get the information from an RFID card inside your pocket or handbag!
These digital pickpockets use RFID card readers to pick the details of your credit or debit cards within a few seconds. Even more disturbing is the fact that they can obtain the data while more than 10 feet away.
But how does RFID card skimming work? Is it a significant security threat?
Well, RFID card skimming is, without a doubt, a security threat. Many organizations globally are struggling with data breaches as a result of RFID card cloning. Data theft is becoming more sophisticated as technology advances.
As a result, organizations are adopting data encryption technology and RFID card blockers to enhance the safety of cardholders’ data.
If you’re wondering how criminals manage to skim data from your RFID cards, then we’ve prepared a breakdown of what happens. This is how they do it:
- Criminals Acquire RFID Readers/ Scanners
RFID cards have an embedded RFID chip that stores all the information about the cardholder. If a criminal gets access to this data, they can use it for their criminal activities.
To achieve this, they get an RFID reader/ scanner that releases electromagnetic waves that excite the RFID card to release data.
In case they want to skim your credit/debit card data, the criminals can insert the illegal card readers inside the ATMs to collect your data and your secret PIN or password.
- Make RFID Card Clones
When the data is released, they will collect and copy it into a blank RFID card to make a clone. These clone cards work exactly like the original cards.
- Use the Clone Cards for Criminal Activities
Once the criminals make a clone card, they can use it to withdraw money from your accounts and make online payments.
Additionally, these criminals can sell the data to other criminals for use in fraudulent activities.
Why You Need RFID Card Blockers
If you’re worried about your data’s security when using RFID-enabled cards, then RFID card blockers will protect you.
These card blockers are made from materials that block radio waves from RFID readers. As such, you can be sure that RFID readers cannot collect the data unless you first remove the card from the blocker.
RFID card blockers come in different forms. Some of the most commonly used RFID blockers include RFID blocking wallets and sleeves.
Types of RFID Card Blockers
- RFID Blocking Wallets
If you’re looking for an efficient way to protect many RFID cards from electronic fraudsters, then an RFID blocking wallet is the best option. These wallets are made of an aluminum case or any other RFID blocking material.
They come in different shapes and sizes. You can be sure that the RFID blocking modifications do not compromise on design. You’ll have a plethora of design options to select from.
- RFID Sleeves
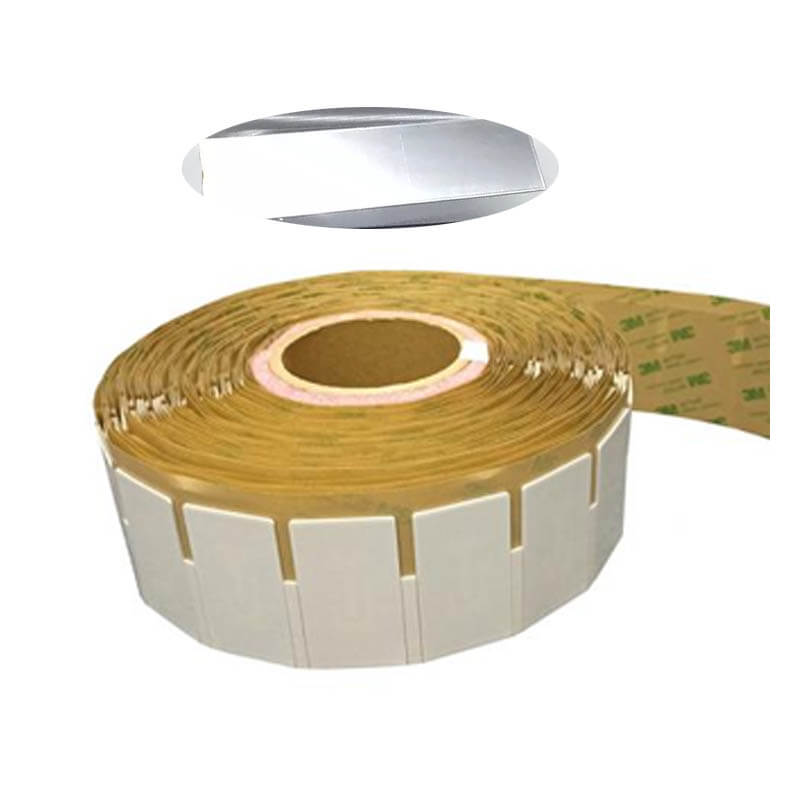
These storage sleeves are small enough to fit in any wallet. They are made of different materials for diverse functions. Some of the most common RFID sleeves include:
- RFID PET Blocking Sleeve. These sleeves are made from a PET material and aluminum foil to block all radio waves from an RFID reader. The PET construction gives the sleeves anti-demagnetization and waterproof abilities. This way, you can be sure that the cards are durable, regardless of the environment. Even better, the sleeves come in different sizes, colors, and designs; and they are also affordable.
- RFID Paper Blocking Sleeve. These sleeves are made of paper material and have a metallic interior to block RFID signals. They have anti-demagnetization and waterproof abilities.
The choice you make depends on your preferences. Ensure that you choose an RFID sleeve that suits your needs. Even better, you can ask for customization from your RFID dealer to get the best deal.
- Faraday Cage/ Faraday Shield
This is a box that encloses all your RFID-enabled items. It is designed to block electromagnetic fields, thus preventing criminals from using RFID readers to skim your cards. They are made of different exterior materials and several layers of RFID blocking material in the interior.
The Faraday box is vital if you use keyless fobs for your car. The fobs have an RFID chip that sends out radio signals. Once your car detects the signals, all the doors will unlock. Keyless ignition also works similarly.
Criminals can use RFID relay boosters to pick up your key fob’s signals and trick the car that the key fob is nearby. As a result, the thieves will access your car and steal. In case your car has keyless ignition systems, they will also steal your car.
However, storing your keyless fobs in a Faraday box blocks the RFID signals from going outside the box. As such, the criminals cannot amplify the signals, and your car will be safe.
These cards integrate a shielding module between PET films and covering material (can be PVC, PET, or ABS). They work by creating a surrounding electromagnetic field that makes all RFID cards invisible by nearby RFID readers.
All you’ll need is to place one RFID blocking card in your wallet, and all your RFID cards will be protected from RFID skimming. Most of the cards have a blocking frequency of 13.56 MHz.