You pay your property manager for an access card. Maybe it costs a few dollars. Maybe it costs twenty. Then one day you hear that someone copied the same kind of card with a phone in a matter of seconds. Or worse, someone bought a cheap reader online and managed to unlock elevator access across an entire building.
That sounds absurd until you look at how many access systems are actually built.
In my experience, the weakness is rarely “magic hacking.” It usually comes from a very ordinary combination: old card technology, lazy configuration, and low-cost system design. The result is that a huge number of access cards are exposed long before anyone even tries to attack them.
The card in your pocket is really a tiny computer
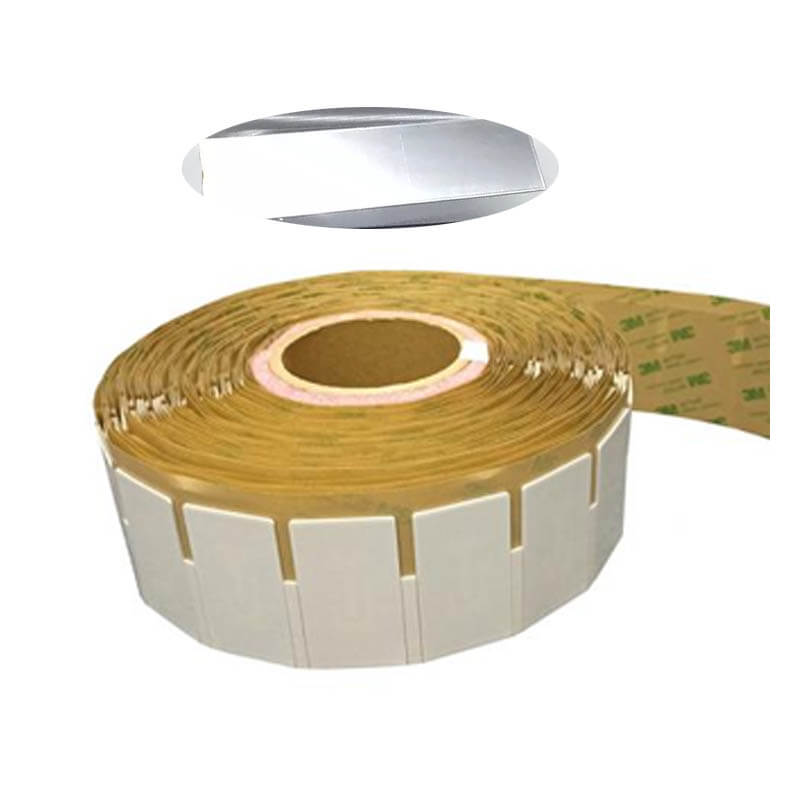
The access cards we use for doors, elevators, and gates are often called IC cards. Many of them rely on NFC-style short-range communication or closely related contactless smart card technology.
Inside the card, there are two important parts:
- A tiny chip
- A coiled antenna
The card has no battery. When you bring it close to a reader, the reader creates an electromagnetic field. That field induces a small current in the card’s antenna, which powers the chip for just long enough to communicate.
At that point, the card and the reader start exchanging data. If the system accepts the card’s identity or credentials, the door opens.
That sounds clean and modern. The problem starts when the “credential” being checked is far too easy to copy.
Why so many cards can be cloned so easily
A huge number of buildings still use MIFARE Classic 1K cards or compatible versions. These cards became popular because they were cheap, widely available, and easy to integrate.
For property operators, that made deployment simple. For attackers, it made life simple too.
Here are the three most common reasons these cards end up effectively unprotected.
1) The system only checks the card number
This is the most common and most careless setup.
Many access systems verify only the card’s UID, or unique identifier. That is like building a login system that asks only for a username and never asks for a password.
If the reader trusts the UID alone, then copying or simulating that UID may be enough to gain access.
Why this happens:
- It is fast to deploy
- It reduces setup complexity
- It avoids real key management
- It works “well enough” until someone tests it
From an operator’s point of view, this shortcut saves time. From a security point of view, it removes the actual security layer.
2) Default keys stay in place for years
Even when the system stores data in protected sectors of the card, many deployments never change the factory keys.
That means the card technically supports access control, but the keys protecting it are still the same ones everyone already knows.
This is one of the most frustrating problems because it is so avoidable. A system can look encrypted on paper while offering almost no real protection in practice.
Typical mistakes include:
- Using factory default sector keys
- Reusing the same keys across the whole property
- Never rotating keys after installation
- Letting vendors deploy “temporary” settings that become permanent
Professional advice: encryption without key management is not meaningful security.
3) The underlying algorithm has known weaknesses
MIFARE Classic relies on Crypto1, an encryption scheme that has been considered broken for many years.
That matters because once a technology’s cryptographic foundation is publicly understood and widely attacked, the barrier to exploitation drops fast. Attackers no longer need elite tools or deep expertise. Cheap consumer devices and public software can do much of the work.
There is another problem: some cards use weak random number generation during the authentication process. That weakness can make it easier to recover keys and expand access from one known sector to the rest of the card.
This is why low-cost “Universal decoder” style devices have become so effective against poorly configured access cards. The system is not failing because NFC itself is unsafe. It is failing because an outdated card platform is being trusted far beyond its actual security level.
Why does a copied card sometimes stop working?
Some people manage to copy an elevator card to a phone, test it once, and then discover that neither the copied version nor the original card works properly afterward.
That usually points to a system using a rolling code or changing credential mechanism.
Here is the basic idea: every time the card is used, the system updates a value stored on the card or in the backend. The next valid transaction depends on that updated value.
If someone copies the card before the value changes, the copy contains old data. Once one version is used, the other version may become out of sync.
That can lead to a few outcomes:
- The copied card stops working
- The original card stops working
- The system flags both as invalid
- The property office has to reissue the credential
From a building management perspective, this is one way to discourage unauthorized duplication. From a user’s perspective, it can feel like the system “killed” both cards.
This is also why a successful copy does not always mean a stable copy. In many systems, cloning identity is easier than maintaining valid state.
Why bank cards and transit cards are a different story
People often assume that if one card can be copied, all cards can be copied.
That is not how it works.
High-security cards such as payment cards and many transit cards typically use CPU cards or other more advanced secure elements. These are much more sophisticated than simple memory cards.
A CPU card is not just storage. It has its own processing capability, security logic, and stronger cryptographic design.
That gives it several advantages:
- Stronger authentication
- Better key isolation
- More secure transaction handling
- More resistance to straightforward cloning
In real-world deployments, these cards are paired with secure backend systems, transaction controls, and anti-fraud mechanisms. That is why casually changing a stored balance or cloning a payment credential is far more difficult than copying a weak door card.
The gap is not small. It is fundamental.
The real problem is not the card alone
It is tempting to blame the card manufacturer, the property office, or the installer. Sometimes all three deserve some blame.
But the deeper issue is that many access control projects prioritize the wrong things.
They optimize for:
- Lowest cost
- Fastest installation
- Broadest compatibility
- Easy replacement
- Simple fee control
They do not optimize for resilience against cloning, credential abuse, or long-term lifecycle security.
That is why so many access systems feel fragile. They were never designed with serious adversaries in mind. They were designed to be cheap, manageable, and “good enough” for daily use.
And for years, that was enough.
What does a safer access system look like?
A safer system does not rely on one trick. It uses multiple layers that work together.
Here is what responsible deployment usually includes:
Stronger credential technology
Use more secure card architectures instead of relying on legacy MIFARE Classic-style deployments for sensitive access control.
Real cryptographic key management
Change default keys, segment permissions correctly, rotate credentials when necessary, and never let convenience override security basics.
Backend verification
Do not trust only what is stored on the card. Validate credentials against backend rules where appropriate.
Anti-copy logic
Use transaction counters, dynamic authentication, or other mechanisms that make static cloning unreliable.
Operational discipline
Even a strong card becomes weak when installers reuse keys, skip provisioning steps, or deploy identical settings across multiple sites.
In my experience, the last point is where many projects fail. The technology may be acceptable. The implementation is what collapses.
Why your team should care
If you manage a property, retail space, warehouse, or office building, weak access credentials create more than a technical problem.
They create:
- Unauthorized entry risk
- Tenant trust issues
- Elevator abuse
- Higher reissuance costs
- Operational headaches for staff
That is why this conversation should move beyond “Can someone copy the card?” The better question is: What assumptions is our system making, and are those assumptions still safe today?
Because once cheap tools and common phones can challenge those assumptions, the old comfort disappears fast.
The bottom line
Many access cards look weak because, in practice, they are weak.
Not because contactless technology is broken. Not because every card can be cracked. And not because every attacker is highly skilled.
They are weak because many systems still rely on outdated MIFARE Classic cards, UID-only verification, factory keys, or poorly implemented security controls. In those environments, the card is practically exposed before it ever reaches your pocket.
Truly secure systems work differently. They use stronger card architecture, better encryption, tighter key management, and a backend that does more than simply trust a number read from a chip.
That is the difference between an access card that only feels secure and one that is actually built for modern risk.
A practical note: using phone-based card emulation for your own convenience may sound harmless, but unauthorized copying or use of access credentials can violate property rules and local law. In the end, the real protection around a building still depends on both technical controls and responsible management.