RFID access control system allows determines who enters or leaves specific premises at any given time. It includes an automated system that identifies an individual, authenticates their details, and allows access upon verification.
The system is designed to only allow specific individuals to access a building. These individuals must possess an RFID card, RFID key fob, RFID wristband, or any other form of RFID tag containing their verification details.
If that sounds confusing, then you shouldn’t worry! This article offers a comprehensive guide on how RFID access control systems work.
What is an RFID Access Control System?
RFID is an acronym for Radio Frequency Identification. This is a system that uses radio waves to transmit information.
A complete RFID system must have a reader and a tag. The tag should preferably be writable and readable for you to write unique details about a specific individual.
Additionally, the write/read attribute allows you to use a single tag for different individuals at different times. For example, when an employee resigns, you can easily erase their data and write fresh data for a new employee.
For an RFID access system to work optimally, it must have all the components listed below:
Components of an RFID Access Control System
- The Server. This component controls the whitelist (a list of all individuals allowed to access a given premise). The system is controlled by the management by typing/saving credentials of all expected visitors.
- Credentials. These are specific details that an organization opts to use for visitors/employee identification. It can be anything ranging from unique PINS, Identity Card Numbers, and Unique Codes among others. There is no standard for credentials and the data to use is solely determined by the management.
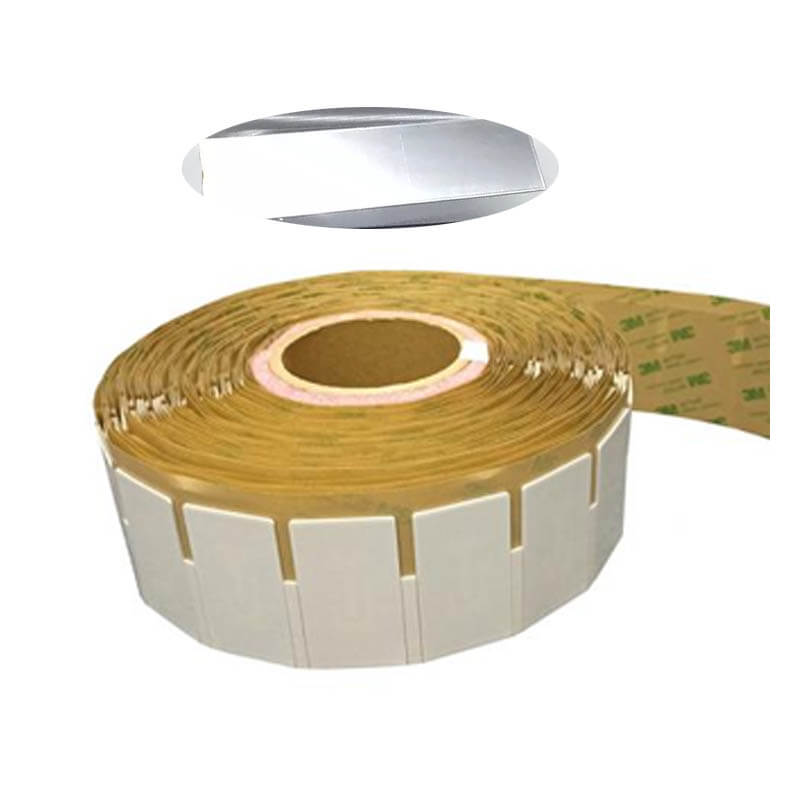
- RFID Tags. This component is where the credentials are stored. The details written on the tags must be an exact match of the details on the whitelist. Any mistake in copying the data will lead to the rejection of the tag by the readers. The tag can be attached to anything including cards, key fobs, bracelets, and wristbands.
- RFID Reader. An RFID reader must be placed strategically to scan RFID tags. If the information stored in the tag matches that on the system’s database, the tagged user will be allowed access.
- Controller. This component compares the data captured by the RFID reader with the information stored in the whitelist. It sends a signal to the door lock to open only if the credentials match.
- Door Lock. RFID door lock system is automated and fully dependent on the controller. The control panel will either send open/close signals. Upon receiving these signals, the door will either open or remain closed, depending on the type of signal received.
While this may appear like a long process, it is lightning-quick! The entire process of identification takes a few seconds!
How RFID Access Control Works
RFID access control system functionality can be simplified in 2 simple steps:
- Data Presentation
- Data Authorization/ Authentication
Data Presentation
This is the initial phase of access control. It requires that data is presented to the RFID reader for analysis.
The data can be presented in various forms depending on the needs and preferences of the management. However, the encoded data must be unique to specific employees. Data duplication will result in errors that may delay admission.
Data presentation follows the following steps:
- Updating Data on the Control System. The control system is the key decision-making component of an RFID access control system. It is the memory of the organization. It stores all the data required for admission into the premises. The management must update it with the credentials of expected visitors.
- Writing RFID Tags. Once the management determines the data combination to use in the control system, it must transfer the exact data to an RFID tag. The tag is then attached to an object such as a card, key fob, or badge.
- RFID Card Presentation. The expected visitor must have an RFID card (or any other object of choice containing their unique RFID tags).
You should note that most RFID control systems are highly automated. You are unlikely to get an assistant at the door. However, the RFID reader will immediately detect your RFID tag and open the door for you to access the premises without restrictions.
Data Authorization
This is the final stage of RFID control systems. It involves data analysis and authentication. The system has a control panel with a memory containing the details of all expected visitors/ employees.
When an individual approaches the door, the following sequence of events happens:
- The RFID Tag Is Powered. The RFID reader, usually positioned at the door, releases electromagnetic signals. When the tag receives these signals, it is powered and sends the saved information to the reader.
- RFID Reader Receives Data. The reader comes with an antenna that receives and transmits data. Immediately it receives the data, this reader will send it to the control panel for analysis.
- Data Comparison. When the control panel receives data from the reader, it scans through its database. If the data sent matches any other data available on the whitelist, the door will open automatically.
If any of these actions is interrupted, the system will not work. In case you experience difficulties gaining access despite having a valid RFID card, then you will need to inquire from the management. The two possible scenarios would be wrong data copied to the card or a malfunction in the system.
Benefits and Drawbacks of RFID Access Control System
RFID access control systems have numerous security benefits to an organization. They guarantee that only authorized individuals can access the given premises.
It also helps an organization to assign specific roles to specific employees. As such, it is easier to prevent data breaches as employees will be accountable for every action they undertake on duty.
Additionally, RFID cards are durable. It can withstand harsh environments, thus making them more cost-effective than other alternatives such as barcodes.
However, RFID access systems have several drawbacks too. For example, there are chances of the system being hacked which can lead to the leaking of private data. They can also be cloned in case hackers get details about the card. Fortunately, the RFID tags can easily be deactivated, thus averting the fear of use by cybercriminals.
Related articles:
- Why You Need RFID Jewelry Tags?
- Use of RFID Technology in Hospitals – 7 Things You Can Track
- A Guide to RFID Tags Types And What are they Difference
- 10 Ways RFID Technology is Already in Your Life!
- RFID on Metal: A Few Things You Should Know about RFID and Metal Surfaces
- Tool Tracking – RFID Tags for Tools
- What is RFID Asset Tracking & How Does It Work?